A Year in Review: The State of Phishing and Best Practices
In 2025, phishing attacks surged, with sophisticated tactics targeting various sectors, particularly financial institutions, educational institutions and SaaS companies, leading to significant financial losses and data breaches.
Push Security reported a trend toward omni-channel phishing published on December 15, 2025, in their annual “Top Phishing Trends” report, with approximately one-third of phishing attacks now occurring outside traditional email, especially via LinkedIn DMs, sponsored search results, and private equity fund mimicries.
Real World Scenarios
Harvard University
Over the past year, phishing attacks have continued to evolve in scale and sophistication with targeting employees, customers, and executives across every industry. Examining real-world phishing incidents from the year highlights how attackers are adapting their tactics, and where organizations are remaining most vulnerable.
In early November 2025, Harvard University fell victim to a phone-based phishing attack that led to unauthorized access to its Alumni Affairs and Development systems. The incident exposed sensitive data, including contact details, donation histories, and related records and affecting alumni, donors, students, as well as faculty.
The key details of this phishing attack were:
Attack vector: A phone call phishing scheme targeting university staff, tricking them into providing access credentials or approving illicit access.
The Affected Systems: Alumni and donor database operations.
The Entities impacted: In addition to Harvard, similar targeted phone phishing attempts impacted Harvard’s institutional peers such as Princeton, Columbia, and UPenn, signaling a coordinated approach across elite universities.
The Timeline: Breach discovered on November 18, 2025; public disclosure followed several weeks later.
This incident represents one of the most significant and recent large-scale phishing-related breaches involving targeted social engineering rather than mass email campaigns.
In May 2025, a highly targeted spear-phishing campaign exploited LinkedIn through LinkedIn direct messages focusing on financial executives worldwide by deploying NetBird (a remote-access tool) in multi-stage attacks.
The key details of this phishing attack were:
- Attack vector: LinkedIn direct message (DM) delivery — Attackers used LinkedIn as the entry vector to exploit trust and bypass conventional email defenses.
- The Affected systems: Multi-stage redirect chain, withvictims routed through:
- Google Search
- A redirection domain (e.g., payrailscanaccord)
- A Firebase hosted landing page of the fake “Common Wealth” fund.
- Entities Impacted: Cloudflare Turnstile — A CAPTCHA-like challenge was used to block automated detection mechanisms and ensure real human interaction.
- The Breakdown of the Attack: Adversary-in-the-Middle (AitM) credential theft: After successfully navigating the challenge, victims saw a Microsoft login page. Submitting credentials and MFA approval handed overactive session tokens to the attacker.
The Takeaways
Why it is important to learn from these incidents and ensure responsible personnel are aware of these attacks are because:
- High-value targets are at risk: The incidents targeted strategic personnel and systems amplifying both reputational and financial risks.
- Social-engineering sophistication is increasing: These campaigns bypass traditional email-based defenses, utilizing voice-based phishing and executive impersonation.
- Cross-sector pattern techniques are being implemented: Similar techniques are now being seen across education, finance, and corporate sectors.
Organizations can most effectively defend and mitigate phishing risks by establishing a comprehensive anti-phishing program, and effective strategies to recognize phishing attempts complemented by continuous employee education on proven methods to identify, as well as avoid phishing attempts.
Key Phishing Statistics and Trends
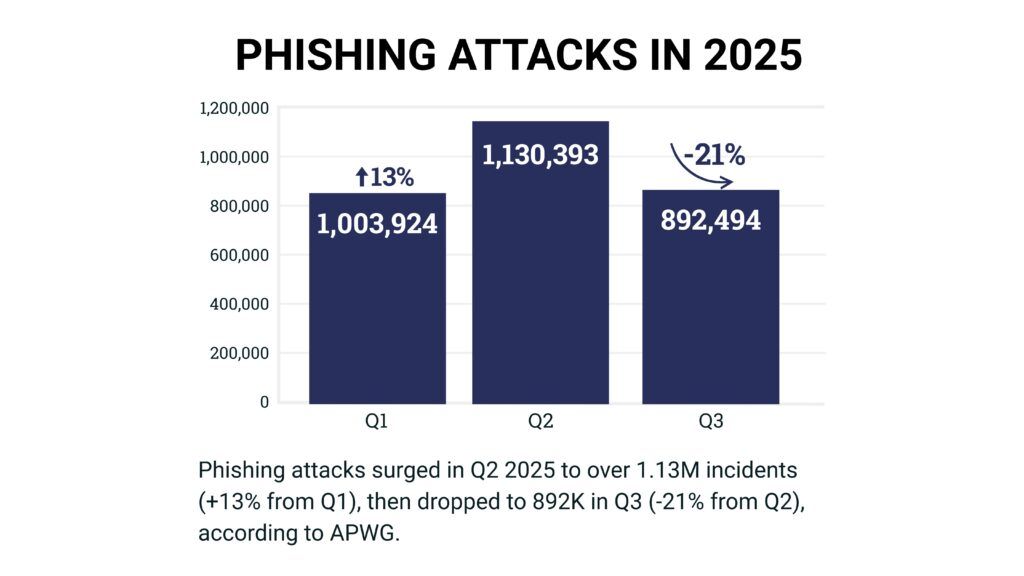
Infographic illustrating phishing attack volumes reported by APWG for Q1–Q3 2025, showing the rise in Q2 and the decline in Q3.
High Volume of Attacks: The Anti-Phishing Working Group (APWG) reported over 1 million phishing attacks in both Q1 (1,003,924) and Q2 (1,130,393) of 2025, marking a 13% increase from the previous quarter. The reported phishing attacks for Q3 werearound 892,494 incidents, a decline from Q2’s peak of 1,130,393.
Financial services and SaaS/Webmail sectors were the most targeted industries.
Common Phishing Techniques
Deceptive Links: This method accounted for 36% of phishing threats, with attackers frequently impersonating well-known brands like Microsoft and Google.
QR Code Phishing: There has been a notable shift towards using QR codes to bypass secure email gateways, making it easier for attackers to lure victims into providing sensitive information.
- Q1 2025: QR‑code phishing increased by 40–60% compared to Q4 2024.
- Source: KnowBe4, blog.knowbe4.com
- Q2 2025: Brands targeted via QR codes: 1,642; DHL and Microsoft were the top two organizations impacted by this type of attack.
- Source: Phishing Activity Trend Reports – APWG, https://apwg.org/trendreports
- Q3 2025: QR code–based phishing: 716,306 unique malicious QR codes detected — +13% from Q2.
- Source: Phishing Activity Trend Reports – APWG, https://apwg.org/trendreports
Identity Hijacking: Techniques such as adversary-in-the-middle (AiTM) and MFA fatigue have emerged, allowing attackers to bypass multi-factor authentication.
- Source: Phishing Activity Trend Reports – APWG, https://apwg.org/trendreports
Financial Impact: Phishing attacks cost organizations approximately $17,700 every minute, with human error contributing to 60% of security breaches.
- Source: IBM’s Cost of a Data Breach Report and industry analyses by Cybersecurity Ventures, https://www.ibm.com/reports/data-breach
Ransomware Links: About 35% of ransomware attacks are initiated through phishing emails, highlighting the critical need for robust email security measures.
- Source: Verizon’s Data Breach Investigations Report (DBIR), https://www.verizon.com/business/resources/reports/dbir/
AI-Driven Phishing: Attackers are increasingly using AI to craft convincing phishing emails, making detection more challenging for traditional security systems.
- Source: IBM X-Force Threat Intelligence Index 2024, https://www.ibm.com/security/xforce
Conclusion
Phishing remained one of the most persistent and adaptive cyber threats throughout 2025, with adversaries continuing to refine their tactics to bypass both human and technical defenses. Notably, newer attack vectors such as QR code–based phishing (“quishing”) and SMS- and voice-based attacks (smishing and vishing) gained significant traction, capitalizing on user trust in mobile devices and the reduced visibility of traditional email security controls. These methods demonstrate a broader shift toward multi-channel social engineering campaigns that are harder to detect and increasingly tailored to specific organizations and roles.
Looking ahead to 2026, organizations should anticipate further convergence of phishing with artificial intelligence, automation, and impersonation techniques, increasing both the scale and credibility of attacks. As a result, maintaining vigilance will require more than point-in-time controls or reactive responses. A comprehensive, defense-in-depth approach is essential to mitigate these evolving threats.
The most effective phishing defense strategies combine continuous user education with measurable testing and layered technical controls. Regular phishing simulations and security awareness programs help reinforce employee readiness and identifyhigh-risk behaviors before they are exploited. Training should emphasize how to recognize suspicious emails, links, QR codes, text messages, and unsolicited phone calls, while clearly defining reporting procedures to ensure rapid escalation and response.
In parallel, organizations should strengthen technical safeguards, including advanced email and messaging security, URL and attachment analysis, mobile device protections, and identity-based controls such as multi-factor authentication. Together, these measures help reduce the likelihood of successful compromise and improve organizational resilience as phishing threats continue to evolve into 2026 and beyond.
Proactive Defense Strategies for Modern Phishing Threats Implementing strong email security
- Use advanced email filtering with AI-based threat detection.
- Enable DMARC, DKIM, and SPF to prevent email spoofing.
- Block known malicious domains and IP addresses.
Multi-Factor Authentication (MFA)
- Require MFA for all critical systems and accounts.
- Even if credentials are stolen, MFA adds a strong layer of protection.
Zero Trust Architecture
- Apply least privilege access and continuous verification.
- Segment networks to limit lateral movement if an account is compromised.
Regular Software Updates & Patching
- Keep operating systems, browsers, and security tools up to date.
- Vulnerabilities often serve as entry points for phishing-related malware.
Use Anti-Phishing Tools
- Deploy browser-based anti-phishing extensions.
- Implement real-time URL scanning and sandboxing for attachments.
The overarching key is to teach and educate staff to recognize suspicious emails, links, social engineering attempts and QR code phishing attempts through continuous security awareness training, phishing simulations and multi-channel phishing scenarios.
The industry is understanding that social engineering is evolving as attackers are moving beyond email to phone calls, QR codes, and LinkedIn messages. The human factor is growing as the weakest link; even strong technical controls fail when employees are deceived into granting access. The speed in incident response also matters. Organizations should implement real-time monitoring and rapid escalation protocols but not overlooking segmentation as an approach to reduce the possible impact.
Tevora Resources
For a deeper dive on email phishing, check out our webinars:
The Scary Side of Cybersecurity: Why On-Premise Penetration Testing is Key
Threat Hunting in the Age of AI: Before and After the Advent of Artificial Intelligence
The Future of Cyber Insurance: A Proactive Approach to Cyber Threats
Additional Resources
For specific Threat related content, check out our resources page.
We Can Help
If you have questions about phishing or would like help harden your organization against these potentially devastating attacks, just give us a call at (833) 292-1609 or email us at [email protected].




