Rethinking Patch Timelines: Defending Against Fast-Moving AI Threats
What is the deal with outdated patch timelines? AI-powered tools have made it easier and cheaper for attackers to create sophisticated exploits, and yet the cost of defending against these threats remains high. For organizations, this makes timely patching endpoints and critical systems a top priority.
In this blog, we break down why traditional patch cycles are outdated, the dangers of delaying updates, and a modern, risk-based framework to protect your organization.
Why Traditional Patch Cycles Fail
Most organizations rely on Patch Tuesday, updating systems once a month. While convenient, this approach leaves gaps:
- Vulnerabilities are publicly disclosed on release days, giving attackers a head start.
- AI makes it possible to develop an exploit in as little as an hour, often at minimal cost.
- Waiting weeks to patch critical systems can be catastrophic.
Takeaway: Exploits don’t wait for your schedule, and neither do attackers.
The Case for Faster, Risk-Based Patching
Endpoint patching is now widely available and often automated, yet many organizations still operate with outdated timelines. A smarter strategy considers:
- Criticality of the system. Not all systems are equal; mission-critical systems or those with sensitive data need faster updates.
- Some updates fix general bugs, while others address known vulnerabilities actively exploited in the wild.
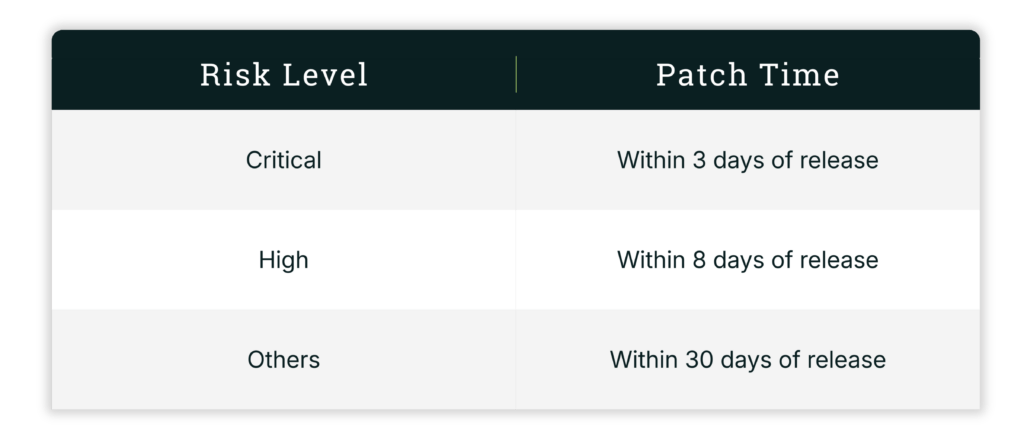
Based on these factors, here’s a recommended patching timeline:
Continuous, Automated Remediation: The Next Step
To stay ahead of modern threats, organizations should evolve from periodic patching to a continuous, automated patch cycle. This approach combines automation with risk-based prioritization, allowing patches to be applied as soon as they are released while focusing first on patches targeted vulnerabilities that are most exploitable or impact critical business systems. Continuous patching not only reduces manual effort for IT teams but also supports high-risk vulnerabilities being addressed immediately, minimizing the window of opportunity for attackers. By embedding automation and continuous monitoring into the patching process, organizations can maintain a proactive security posture and prevent the scramble that often follows when standards or frameworks tighten patching expectations.
How AI Changes the Threat Landscape
Artificial intelligence has shifted the cyber risk landscape dramatically. Exploit automation allows attackers to generate attacks in minutes after a CVE release. AI-driven methods bypass traditional defenses with minimal human effort, while attackers can simultaneously target multiple systems. These factors make it clear that traditional patching strategies can no longer be kept up.
Calendar Days vs. Business Days: Why It Matters
Many organizations calculate patch timelines on business days, but vulnerabilities don’t pause weekends or holidays. Treating patch deadlines as calendar days ensures that systems remain protected continuously, without gaps over off days. This approach allows security teams to respond immediately to newly disclosed vulnerabilities and reduces the window of opportunity for attackers. In today’s fast-moving threat landscape, every hour counts, making calendar-day timelines a practical and essential strategy for minimizing risk.
Benefits of Accelerated, Risk-Based Patching
Implementing a faster, risk-based patching strategy offers significant advantages. It reduces exposure to known vulnerabilities, helping organizations stay one step ahead of attackers, particularly those leveraging AI-enabled tools to create exploits in hours. By focusing on critical systems and high-risk updates, organizations can protect the most sensitive assets and reduce the likelihood of costly breaches. Additionally, a well-managed patching process supports compliance with regulatory requirements and demonstrates diligence to auditors. Overall, adopting an accelerated, risk-based approach strengthens an organization’s cybersecurity posture and ensures that defenses remain resilient in an increasingly complex threat landscape.
Conclusion
In today’s threat landscape, waiting weeks to patch critical systems is no longer acceptable. Organizations need to evolve beyond simple calendar-based patching and adopt a continuous, automated cycle that prioritizes updates based on exploitability and business impact. By tightening patching windows for high-risk vulnerabilities, building in automation wherever possible, and moving toward ongoing, proactive remediation, security teams can stay ahead of attackers rather than scrambling to catch up once frameworks or standards shorten their timelines. Adopting this approach not only reduces exposure to AI-powered exploits but also strengthens the organization’s overall cybersecurity posture, ensuring critical systems remain protected, and compliance requirements are consistently met.




